By
Gigabit Systems
April 24, 2026
•
20 min read
Why You Need to Secure Both Today
Most people think their bank account is the most important thing they need to protect.
It is not.
It is their email and their phone number.
These two things control access to almost everything else.
If an attacker gets into either one, they are not just accessing a single account. They are gaining control over your entire digital identity.
The Weak Point Nobody Realizes
Your personal email is one of the weakest security points in your life right now.
Your phone number is right behind it.
Most people:
Reuse passwords
Do not use proper MFA
Rely on SMS for security
Assume nobody is targeting them
That combination is exactly what attackers are counting on.
How Hackers Actually Get In
The attack rarely starts with your email.
It starts somewhere else.
A shopping site gets breached
A forum gets breached
A travel site gets breached
A social app gets breached
Your email and password are stolen and added to massive credential lists.
From there, attackers run automated login attempts across:
Email providers
Banking platforms
Cloud services
Business systems
This is called credential stuffing.
It works because people reuse passwords.
If you used that same password for your email, the attacker does not need to hack anything.
They simply log in.
Why Email Access Is So Dangerous
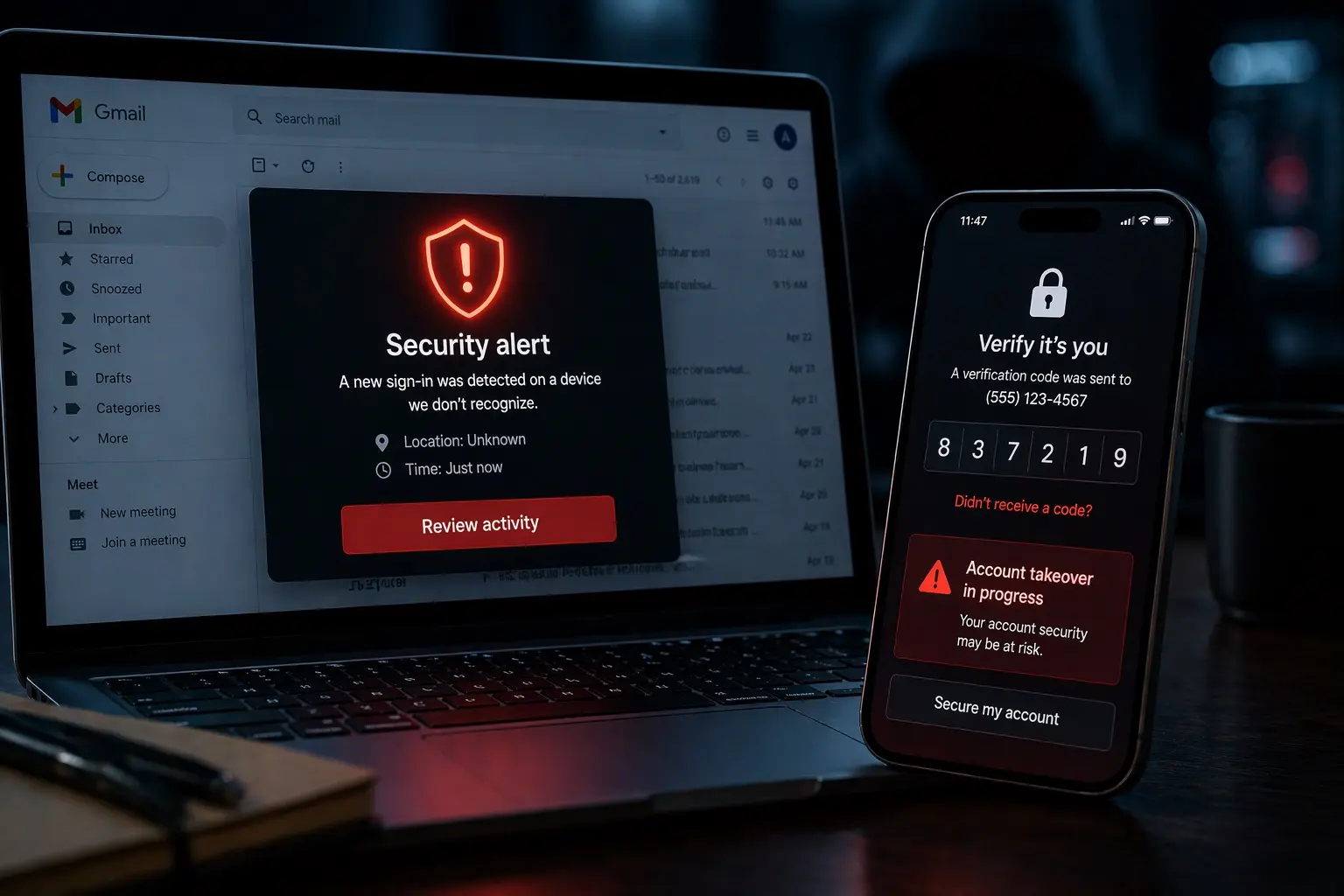
Once attackers control your email, they control your reset path.
They can reset access to:
Banking
Credit cards
Cell carriers
IRS and tax portals
Shopping accounts
Cloud storage
Business tools
They intercept the reset emails.
They approve the login attempts.
They lock you out.
From there, they begin rebuilding your identity around themselves.
Where Your Phone Number Comes In
Your phone number is tied directly into this process.
It is used for:
Two-factor authentication
Account recovery
Identity verification
If attackers take control of your number through SIM swapping, they receive your:
Verification codes
Password reset texts
Security alerts
At that point, your accounts are no longer yours.
What SIM Swapping Really Is
A SIM swap attack is simple.
An attacker calls your carrier pretending to be you.
Using data from breaches and social media, they convince support to transfer your number to a SIM they control.
Your phone goes dead.
Their phone becomes you.
No hacking tools.
No malware.
Just social engineering.
Why This Spirals So Fast
Once attackers control both your email and your phone number:
They reset everything
They bypass MFA
They take over financial accounts
They open new accounts in your name
This is how identity theft becomes unstoppable.
If You Still Use Yahoo or AOL, Move
If your primary email is still on Yahoo or AOL, it is time to move.
These platforms have a long history of large-scale breaches.
Modern providers like Gmail offer:
Stronger authentication options
Security checkups
Device monitoring
Passkeys
Better protection against outdated access methods
You can secure almost anything.
But starting from a stronger platform matters.
Step-by-Step: Lock Down Your Gmail
1. Change Your Password
Make it long
Make it unique
Never reuse it
Use a password manager.
2. Enable 2-Step Verification
Use:
Security key (best)
Authenticator app (strong)
Avoid relying on SMS
3. Add Passkeys
Reduce reliance on passwords entirely.
4. Review Recovery Options
Make sure:
Recovery email is yours
Recovery phone is yours
No old or unknown entries exist
5. Check Logged-In Devices
Sign out anything you do not recognize.
6. Review Security Activity
Look for:
Unknown logins
Recovery changes
Suspicious behavior
7. Remove Old App Access
Revoke anything you do not actively use.
8. Check Gmail Activity Logs
Review access history.
Act immediately if anything looks off.
9. Strengthen Other Accounts
Do not let email be your only recovery method.
Use:
App-based MFA
Unique passwords
Clean recovery settings
10. Run a Full Security Checkup
Do this regularly.
Not once.
Lock Down Your Phone Number
Contact Your Carrier
Enable protections like:
Number Lock
Port Freeze
Account PIN
In-store verification requirement
General Rules
Never use real answers for security questions
Never trust inbound calls
Always call your carrier directly
Assume your information is already out there
One More Layer Most People Miss
On iPhone, use Screen Time as a security control:
Set a separate Screen Time passcode
Block account changes
Block passcode changes
Even if someone gets into your phone, they cannot lock you out.
The Real Problem
Most people secure their work systems better than their personal identity.
That is backwards.
Your personal email and phone number are the gateway into:
Your business
Your finances
Your identity
Bottom Line
Attackers are not breaking in.
They are logging in.
And once they control your email and your phone number, they control everything else.
70% of all cyber attacks target small businesses, I can help protect yours.
#CyberSecurity #IdentityProtection #SMBSecurity #DataProtection #AccountSecurity